Gogo Serving Fake SSL Certificates to Block Streaming Sites
PC Magazine has the article and video Gogo Serving Fake SSL Certificates to Block Streaming Sites.
Mile-high Web provider Gogo appears to be running man-in-the-middle attacks on its own customers.
Based on a report by Google engineer Adrienne Porter Felt, Gogo Inflight Internet is serving SSL certificates from Gogo instead of site providers—a big no-no in online security.
Will someone please explain to me why this isn’t one of the biggest security flaws in the entire design of the secure sockets layer of internet data transport? Surely people who designed and implemented the system considered this form of attack, didn’t they? Surely PC magazine could explain how to protect yourself from this, can’t they?
If GoGo can do this, who is to say who else might not try this?
I cannot even comprehend how the security expert who discovered this could calmly say “serving SSL certificates from Gogo instead of site providers—a big no-no in online security.” How could a security expert conceive of a secure system whose security depended on people not cheating? I thought the whole point of security was to stop people from cheating. If you design a system to stop people from cheating that depends on people not cheating, then you must be a fool.
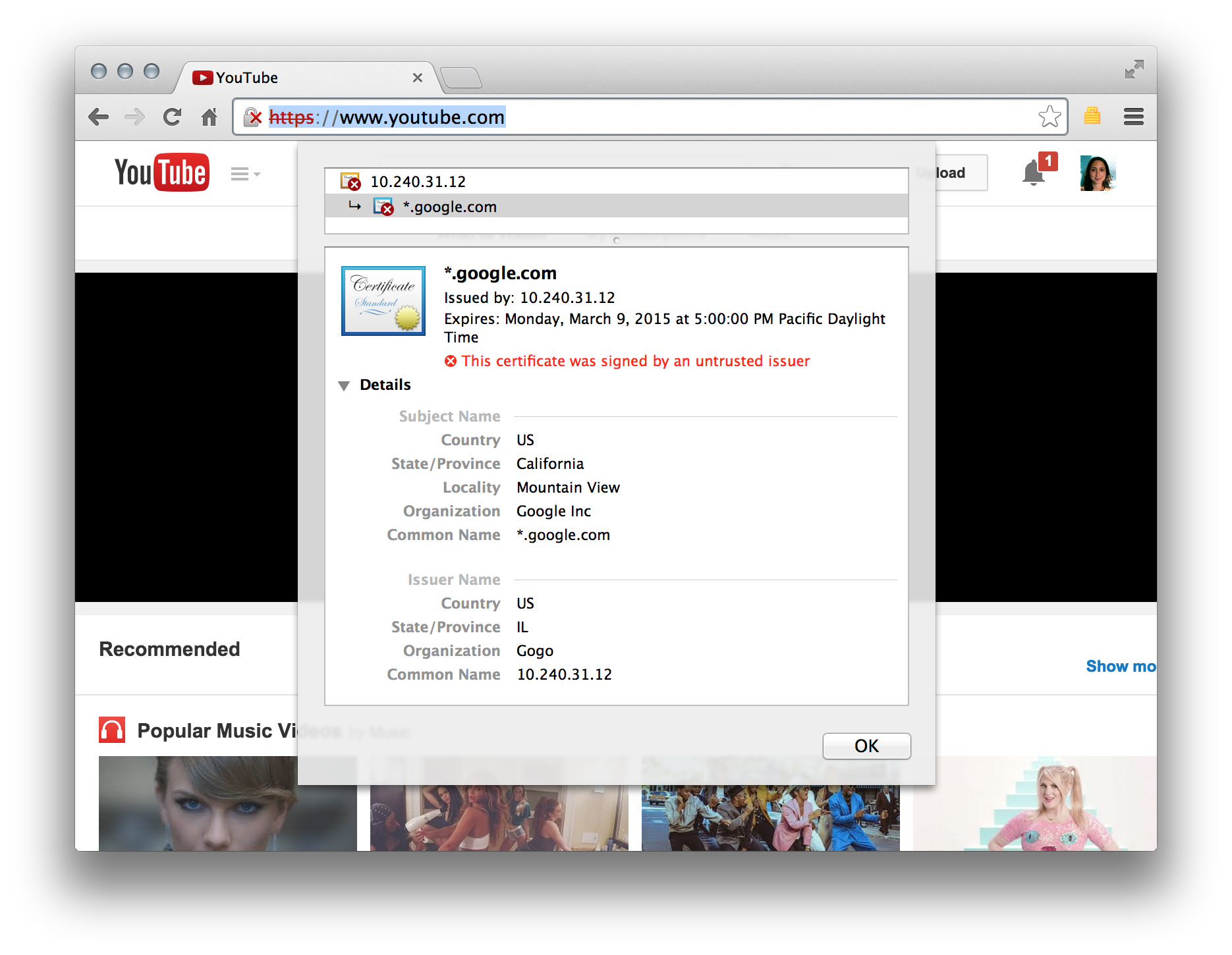
Now, let me step back and try to consider this rationally. If you follow the links in the article, you will eventually see what the discoverer of this fakery saw.
If you look at the, you will see it say “This certificate was singed by an untrusted issuer.” The lesson learned is to never trust an untrusted issuer, duh! However, I have to ask that if every browser is automatically set up to boldly issue such a warning, why haven’t millions of people in the flying public been screaming about this already? Even if most people wouldn’t know what to do with such a message, there must be enough techies flying the friendly skies that many of them would have complained about this before. I am definitely going to research this issue more. This looks like a big, honking hole in internet security.
Some people wonder why we refuse to fly since I have retired. Add this one to the list of reasons.
I would only be flying for pleasure, anyway. So the risk to me is that I might “only” be giving away access to all my financial and health data. Think about all the business travelers who are compromising their companies’ secret information while all along they think they are protecting it.
CertificateTransparency.org has the article What is Certificate Transparency? They first explain the issue:
Thanks to modern cryptography, browsers can usually detect malicious websites that are provisioned with forged or fake SSL certificates. However, current cryptographic mechanisms aren’t so good at detecting malicious websites if they’re provisioned with mistakenly issued certificates or certificates that have been issued by a certificate authority (CA) that’s been compromised or gone rogue.
They prescribe certificate transparency as the solution. Read about it, and see if you feel any safer. Obviously this flaw is well known to anybody who wants to cheat the system.
ZDnet published the article How the NSA, and your boss, can intercept and break SSL in June 2013..
Blue Coat, the biggest name in the SSL interception business, is far from the only one offering SSL interception and breaking in a box.
If the punctuation of that quote is misleading, let me reword it slightly. For a fee, you can buy an SSL interception application without the need to know anything about how that application accomplishes the feat. That’s not even the most disturbing part of what is in the article.
As I think about the description of the interception in the above article, I wonder how GoGo could have been so sloppy that it allowed the browser to detect that ““This certificate was singed by an untrusted issuer.” The only thing I can guess is that the Google engineer who detected this had independent means of checking the authenticity of the certificate that purported to come from YouTube (which is owned by Google.)
January 12, 2015
The Hacker News has the article New Firefox 32 Adds Protection Against MiTM Attack and Rogue Certificates. I am still not convinced.
Stackexchange has the Q & A How do RSA fingerprints protect from MITM attacks?
I posed the following questions to that Q & A:
What about a Man in the middle attack that fakes the public key and the fingerprint of the secure server. In other words, the MITM gives you a public key to use that it has the private key for. It then forwards your message on to the actual recipient by re-encoding your decrypted message with the real public key. It does the same fakery for the message coming back from the secure server.
How do you really know that the public key you are getting is the actual public key of the server you intended to talk to? Yes their are certificate authorities, but if the MITM can fake the public key of your intended target, why can’t it fake what you get from the certificate authority?
I am still not entirely convinced. All the methods that I have read about a secure exchange of information to ensure a secure exchange of information all seem circular to me. If you could have a secure exchange of information to set up a secure exchange of information, then why couldn’t that method be your method of secure exchange? Adding more layers to the protocol may increase the number of things the MITM attacker has to fake, but it is nowhere near the size of the mathematical difficulty that adding more binary bits to the code would present if you could only know for sure that you had a valid public key.